Hackers Stealing Browser Cookies to Hijack High-Profile YouTube Accounts
Since at least late 2019, a network of hackers-for-hire have been hijacking the channels of YouTube creators, luring them with bogus collaboration opportunities to broadcast cryptocurrency scams or sell the accounts to the highest bidder.
That’s according to a new report published by Google’s Threat Analysis Group (TAG), which said it disrupted financially motivated phishing campaigns targeting the video platform with cookie theft malware. The actors behind the infiltration have been attributed to a group of hackers recruited in a Russian-speaking forum.
“Cookie Theft, also known as ‘pass-the-cookie attack,’ is a session hijacking technique that enables access to user accounts with session cookies stored in the browser,” TAG’s Ashley Shen said. “While the technique has been around for decades, its resurgence as a top security risk could be due to a wider adoption of multi-factor authentication (MFA) making it difficult to conduct abuse, and shifting attacker focus to social engineering tactics.”
Since May, the internet giant noted it has blocked 1.6 million messages and restored nearly 4,000 YouTube influencer accounts affected by the social engineering campaign, with some of the hijacked channels selling for anywhere between $3 to $4,000 on account-trading markets depending on the subscriber count.
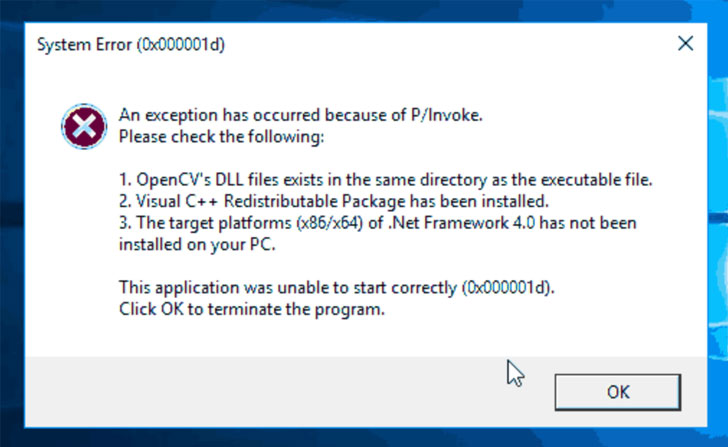 |
| Fake error window |
Other channels, in contrast, were rebranded for cryptocurrency scams in which the adversary live-streamed videos promising cryptocurrency giveaways in return for an initial contribution, but not before altering the channel’s name, profile picture, and content to spoof large tech or cryptocurrency exchange firms.
The attacks involved sending channel owners a malicious link under the ruse of video advertisement collaborations for anti-virus software, VPN clients, music players, photo editing apps, or online games that, when clicked, redirected the recipient to a malware landing site, some of which impersonated legitimate software sites, such as Luminar and Cisco VPN, or masqueraded as media outlets focused on COVID-19.
Google said it found no fewer than 15,000 accounts behind the phishing messages and 1,011 domains that were purpose-built to deliver the fraudulent software responsible for executing cookie stealing malware designed to extract passwords and authentication cookies from the victim’s machine and upload them to the actor’s command-and-control servers.
The hackers would then use the session cookies to take control of a YouTube creator’s account, effectively circumventing two-factor authentication (2FA), as well as take steps to change passwords and the account’s recovery email and phone numbers.
Following Google’s intervention, the perpetrators have been observed driving targets to messaging apps like WhatsApp, Telegram, and Discord in an attempt to get around Gmail’s phishing protections, not to mention transitioning to other email providers like aol.com, email.cz, seznam.cz, and post.cz. Users are highly recommended to secure their accounts with two-factor authentication to prevent such takeover attacks.





